




Price: $18.09
(as of May 11, 2024 12:47:37 UTC – Details)
Product Description


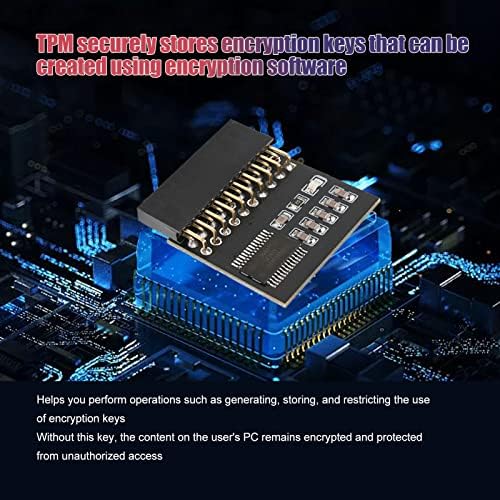
Unlock a new level of security with our dedicated cryptographic processor, the TPM module. Intricately connected to the motherboard’s daughter board, this module functions as an independent cryptographic processor, safeguarding encryption keys with precision.Rest assured, our TPM1.2 encryption security module finds common application across diverse motherboard brands. However, it’s important to note that certain motherboards may require the insertion of a TPM module or BIOS updates to activate the TPM option.Designed for stability and durability, our TPM module is constructed with a reliable PCB material. This ensures a product that epitomizes stability in performance, resulting in heightened work efficiency and seamless operation.One of the key advantages of our TPM module is its versatility. As a fortified cryptographic processor, it excels in performing a range of operations. From key generation to storage and even imposing usage restrictions on cryptographic keys, this module is a powerful tool in enhancing your system’s security.
Specification:
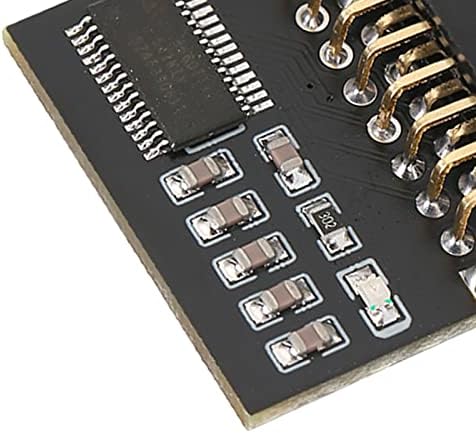
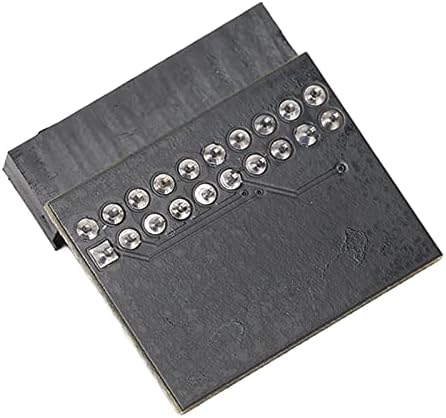
Item Type: TPM 1.2 Encryption Security Module Material: PCB Colour: Black TPM Version: TPM 1.2 Number of Pins: 20pin Packing List: 1 x TPM 1.2 Encryption Security Module
Dedicated Cryptographic Processor: The TPM functions as an independent cryptographic processor intricately connected to the motherboard’s daughter board. Safeguarding encryption keys is its forte, and it seamlessly accommodates keys generated through encryption software.
Enhanced Security: With the key held securely, content stored on the user’s PC remains under wraps, impervious to unauthorized intrusion. This layer of protection guarantees the of sensitive information.
Broad Utility: The TPM1.2 encryption security module finds common application across diverse motherboard brands. Certain motherboards mandate the insertion of a TPM module or BIOS updates to activate the TPM option. It’s important to note that the version in use is TPM1.2.
Stability in Design: Constructed with a reliable PCB material, the TPM module epitomizes stability in performance. This translates to heightened work efficiency, seamless operation, and prolonged durability, ensuring a product that stands the test of time.
Versatile Operations: Functioning as a fortified cryptographic processor, the TPM excels in performing a range of operations. It facilitates key generation, storage, and the imposition of usage restrictions on cryptographic keys.
This post is exclusively published on eduexpertisehub.com


