Price: $59.99 - $33.99
(as of May 03, 2025 07:32:08 UTC – Details)

Power up your Windows security skills with expert guidance, in-depth technical insights, and dozens of real-world vulnerability examples from Google Project Zero’s most renowned researcher!
Learn core components of the system in greater depth than ever before, and gain hands-on experience probing advanced Microsoft security systems with the added benefit of PowerShell scripts.
Windows Security Internals is a must-have for anyone needing to understand the Windows operating system’s low-level implementations, whether to discover new vulnerabilities or protect against known ones. Developers, devops, and security researchers will all find unparalleled insight into the operating system’s key elements and weaknesses, surpassing even Microsoft’s official documentation.
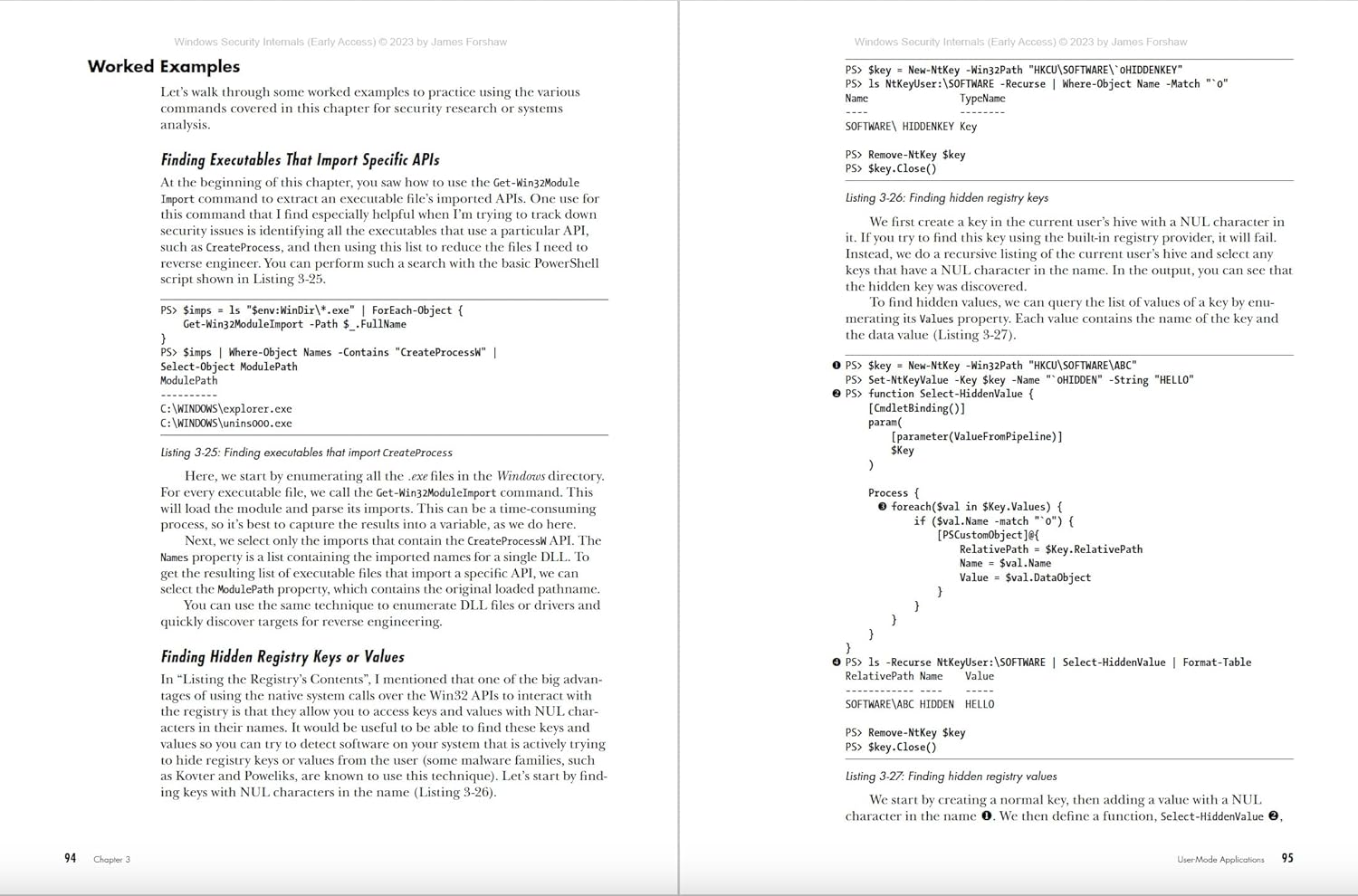
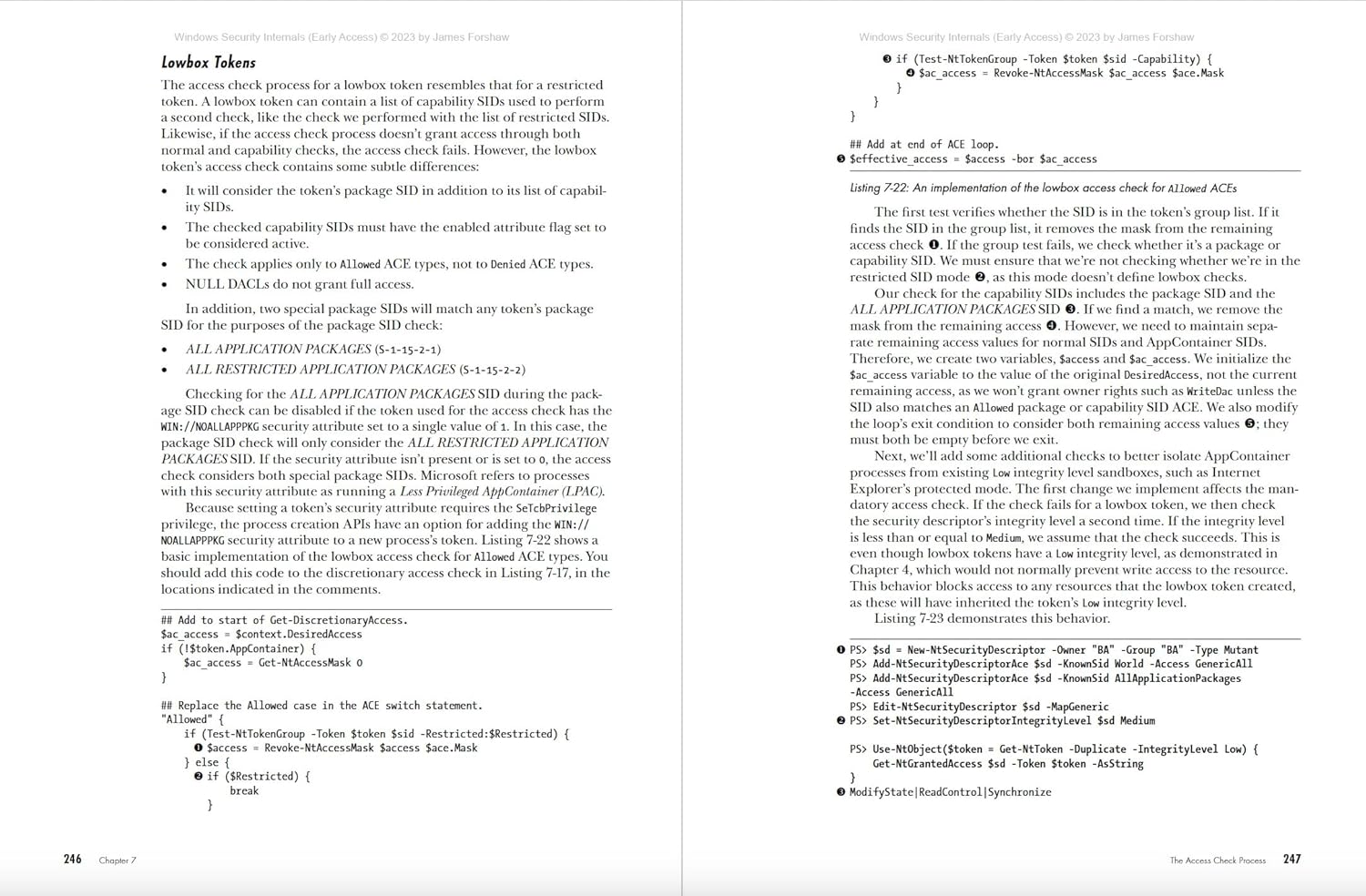
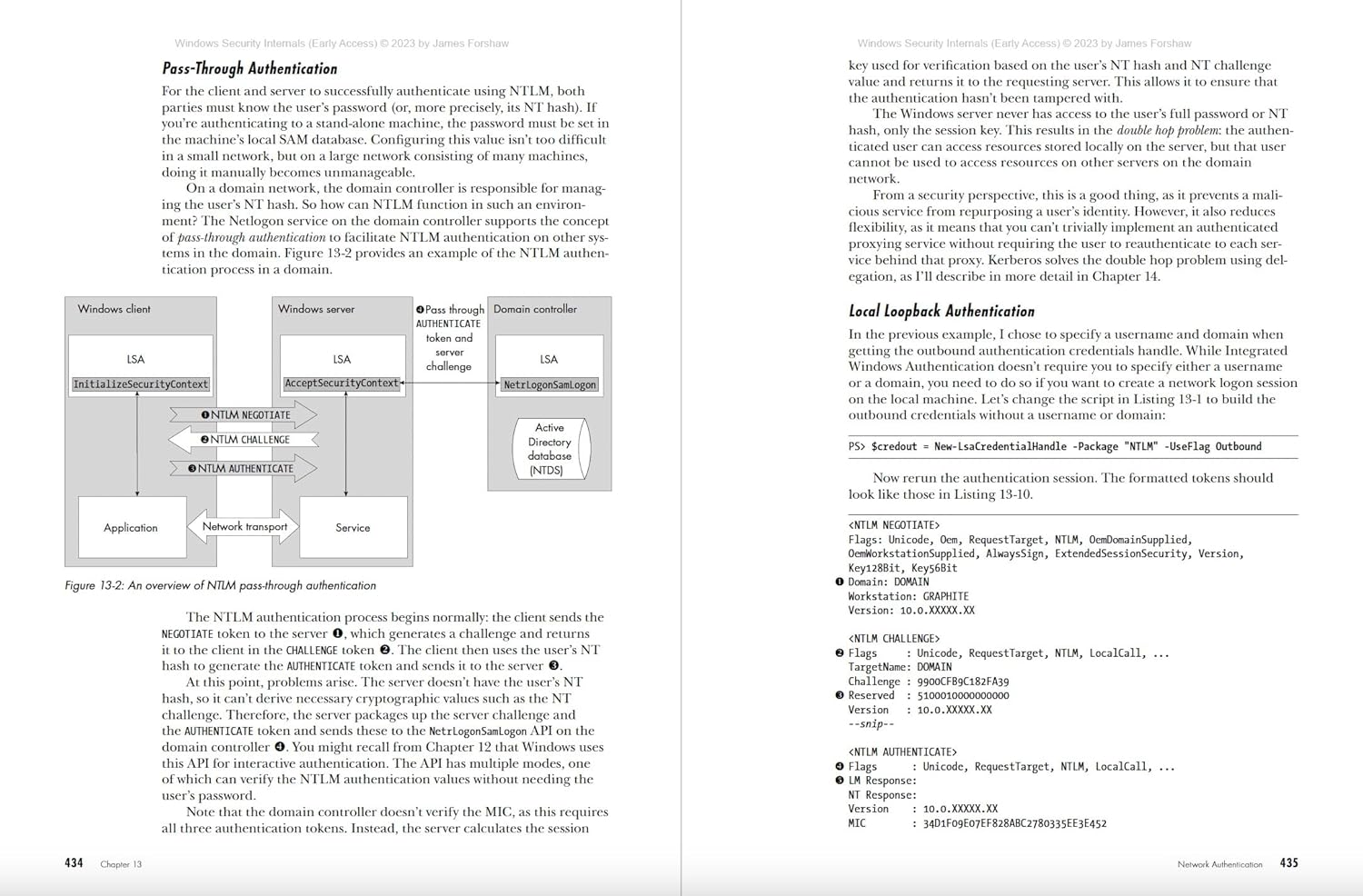
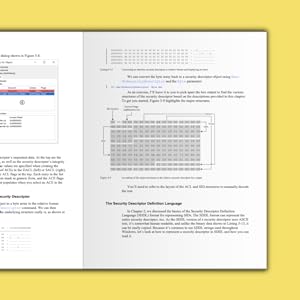
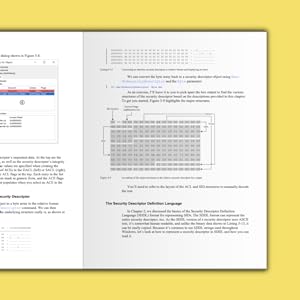
Author James Forshaw teaches through meticulously crafted PowerShell examples that can be experimented with and modified, covering everything from basic resource security analysis to advanced techniques like using network authentication. The examples will help you actively test and manipulate system behaviors, learn how Windows secures files and the registry, re-create from scratch how the system grants access to a resource, learn how Windows implements authentication both locally and over a network, and much more.
You’ll also explore a wide range of topics, such as:
Windows security architecture, including both the kernel and user-mode applicationsThe Windows Security Reference Monitor (SRM), including access tokens, querying and setting a resource’s security descriptor, and access checking and auditingInteractive Windows authentication and credential storage in the Security Account Manager (SAM) and Active DirectoryMechanisms of network authentication protocols, including NTLM and Kerberos
In an era of sophisticated cyberattacks on Windows networks, mastering the operating system’s complex security mechanisms is more crucial than ever. Whether you’re defending against the latest cyber threats or delving into the intricacies of Windows security architecture, you’ll find Windows Security Internals indispensable in your efforts to navigate the complexities of today’s cybersecurity landscape.
From the Publisher
“This book . . . belongs on the desk of every security professional and developer working with Windows security.”
—Jeffrey Snover, Inventor of PowerShell | former Chief Architect for Windows Server
“James Forshaw’s understanding of Windows Security rivals that of some of our best security teams roaming throughout Microsoft. Windows Security Internals hits the mark for being an easy-to-read introductory text and equally advanced to teach even the best security folks a thing or two. This book should be required reading for anyone interested in understanding Windows Security and will be required reading for everyone on our team in the Windows Security org.”
—Steve Syfuhs, Principal Developer, Windows Authentication, at Microsoft
“An invaluable gem of a book! Highly recommended for every security researcher or enthusiast that wants to understand yet undocumented Security perks of the Windows operating system. James is a fountain of knowledge; he explains clearly and concisely, but also very detailed, what you ever wanted to know about Windows security internals.”
—Miriam C. Wiesner, Sr. Security Researcher at Microsoft, author of PowerShell Automation and Scripting for Cybersecurity
About the Author
James Forshaw is a renowned computer security expert on Google’s Project Zero team. In his more than 20 years of experience analyzing and exploiting security issues in Microsoft Windows and other products, he has discovered hundreds of publicly disclosed vulnerabilities in Microsoft platforms. Others frequently cite his research, which he presents in blogs, on the world stage, or through novel tooling, and he has inspired numerous researchers in the industry. When not breaking the security of other products, James works as a defender, advising teams on their security design and improving the Chromium Windows sandbox to secure billions of users worldwide. He’s also the author of Attacking Network Protocols (No Starch Press)


About the Publisher
No Starch Press has published the finest in geek entertainment since 1994, creating both timely and timeless titles like Python Crash Course, Python for Kids, How Linux Works, and Hacking: The Art of Exploitation. An independent, San Francisco-based publishing company, No Starch Press focuses on a curated list of well-crafted books that make a difference. They publish on many topics, including computer programming, cybersecurity, operating systems, and LEGO. The titles have personality, the authors are passionate experts, and all the content goes through extensive editorial and technical reviews. Long known for its fun, fearless approach to technology, No Starch Press has earned wide support from STEM enthusiasts worldwide.
Publisher : No Starch Press (April 30, 2024)
Language : English
Paperback : 608 pages
ISBN-10 : 1718501986
ISBN-13 : 978-1718501980
Item Weight : 2.4 pounds
Dimensions : 7.06 x 1.38 x 9.19 inches